Trezor Login: Secure Access to Your Crypto Wallet
A comprehensive guide for beginners and mid-level users to safely access and manage their Trezor wallets.
Why Trezor Login is Crucial
The Trezor Login process is the gateway to safely accessing your cryptocurrency assets. Unlike online wallets, Trezor hardware wallets keep your private keys offline, minimizing risk of hacks. Logging in securely ensures you can send, receive, and monitor your crypto assets with peace of mind.
Whether you’re new to Bitcoin, Ethereum, or exploring altcoins, understanding the Trezor login process is essential for protecting your digital wealth.
Pro Tip:
Never share your 24-word recovery phrase online or with anyone. Trezor Login requires your device and PIN verification — that’s all you need to safely access your wallet.
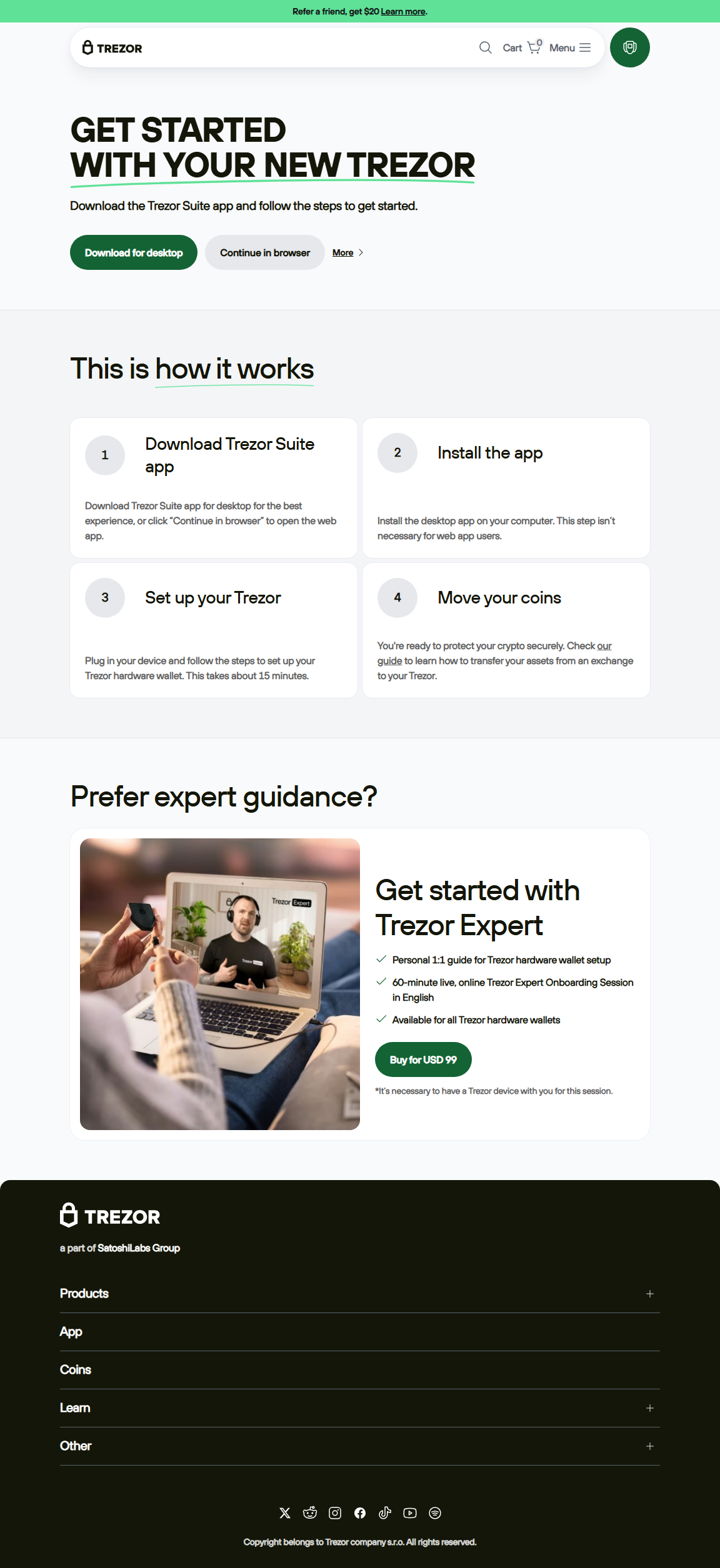
Step-by-Step Guide to Trezor Login
Logging into your Trezor wallet is straightforward. Follow these steps for a secure experience:
- Connect Your Trezor Device: Plug in your Trezor hardware wallet to your computer or mobile device.
- Open Trezor Suite: Launch the official Trezor Suite app or access the web suite.
- Verify Device: Confirm the device’s authenticity using the security check prompts.
- Enter Your PIN: Input your secure PIN on the device itself.
- Access Your Wallet: Once verified, you can view your balances, send/receive crypto, or manage accounts.
Following these steps ensures that your login is secure and your funds are protected from online threats.
Trezor Login vs Software Wallets
| Feature | Trezor Login | Software Wallets |
|---|---|---|
| Security | Offline keys, device verification | Online keys, vulnerable to hacks |
| Ease of Use | User-friendly, beginner-friendly | Varies, sometimes complex |
| Backup & Recovery | 24-word recovery phrase | Password-based or cloud backup |
Tips for Mid-Level Users
- Portfolio Monitoring: Track multiple cryptocurrencies with real-time performance charts.
- Staking: Stake supported coins directly from Trezor Suite for passive rewards.
- Regular Updates: Keep Trezor Suite and firmware updated to prevent vulnerabilities.
- Multi-Account Management: Organize multiple wallets securely under a single device.
Security Highlight
Trezor Login uses a combination of hardware verification and PIN entry. This means even if your computer is compromised, hackers cannot access your funds without physical access to your device.
A Beginner’s Experience
John, new to crypto, was nervous about managing Bitcoin safely. Using the official Trezor Login process, he connected his Trezor Model T, entered his PIN, and accessed his wallet securely. Today, John not only manages Bitcoin but also Ethereum and other altcoins with confidence, knowing his assets are protected offline.
Trezor Login FAQs
Q1: Can I login without my Trezor device?
No. Trezor Login requires your hardware wallet for secure verification. Your recovery phrase cannot be used to log in online.
Q2: Is Trezor Login beginner-friendly?
Yes. The process is straightforward with step-by-step instructions and visual cues in Trezor Suite.
Q3: How do I recover access if I lose my device?
You can restore your wallet on a new Trezor device using your 24-word recovery phrase offline. Never share this phrase online.
Security Reminder:
Always download Trezor Suite from the official source and verify your device during login. Avoid unofficial apps or links that claim to provide Trezor access.
Conclusion
Trezor Login is more than just a way to access your wallet; it’s the cornerstone of crypto security. By following official guidelines, verifying your device, and using Trezor Suite, you ensure that your digital assets remain protected from online threats.
From beginners to mid-level users, Trezor Login provides a secure, reliable, and easy-to-use interface to manage multiple cryptocurrencies safely. Take the first step today and access your wallet with confidence.
Secure your crypto, follow best practices, and make Trezor Login your trusted gateway to the digital finance world.